Ok, we are using Asus in our office, luckily it is not the same model.
“Critical vulnerabilities” were found to exist in three brands of wireless routers sold in the country, according to security company Vantage Point and confirmed by Singapore Computer Emergency Response Team (SingCERT).
At least one Internet Service Provider (ISP) has acknowledged the issue and is working to fix the vulnerability.
In a blogpost on Tuesday (Feb 24), Vantage Point’s Senior Security Consultant Lyon Yang highlighted “critical vulnerabilities” in three brands of routers – Zhone, Aztech and Asus. These vulnerabilities “allow an attacker to become at least a network administrator, and in most cases also gain a remote root shell, with relatively low effort”, he said.
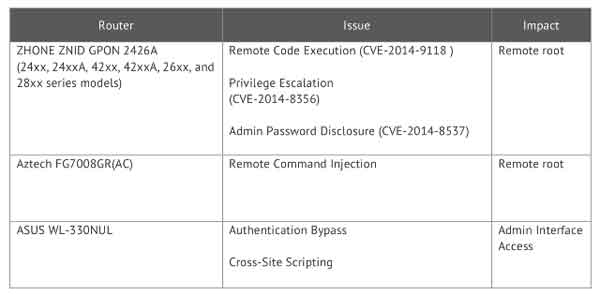
It added that there were several “proof-of-concept exploits” developed based on the vulnerabilities. In other words, the researcher created possible exploits, but there are no known attacks by hackers on affected customers so far.
“There are many routers with many different kinds of firmware on the market. The problem is that when the firmware is developed in-house by the vendor, security is often an afterthought,” Mr Yang told Channel NewsAsia via email.
“Based on our research, up to 32,000 subscribers in Singapore may be affected by the vulnerabilities discovered so far,” he added.
An advisory was posted on the SingCERT’s website on Wednesday evening, confirming the vulnerability. “It is reported that a few routers that may have been provided by Singapore ISPs are found to contain vulnerabilities or insecure configuration,” it stated.
Vantage Point also highlighted that “thousands of ViewQwest users to be particularly vulnerable”. Mr Yang wrote that they use the Zhone GPON router with a “statically assigned Internet Protocol (IP) address with all default services exposed on the Internet”.
Based on the vulnerability, it is possible to compromise these routers “at will” and hackers may obtain the subscriber’s name and residential address. They may also install malware or manipulate the user’s network traffic, according to the blogpost.
In response to Channel NewsAsia’s questions, ViewQwest Chief Operating Officer Chris Williams acknowledged that there is a known security vulnerability with some models of Zhone routers. He added that besides the proof-of-concept testing done by “two concerned customers”, none of its other customers have reported issues with the vulnerability.
The COO added only “a minority” of its customers “use an affected router in a way which is susceptible to the vulnerability identified”.
“We have been working with the vendor to obtain a fix to the vulnerability in their affected routers. In the interim, we have been progressively remediating the problem via another method throughout our customer base. This work is still underway and is expected to be completed by the weekend.,” Mr Williams said.
Telco Singtel is another company that offers the Aztech router highlighted in Vantage Point’s report, according to its website.
Channel NewsAsia has gotten in touch with the other two manufacturers for comments on the vulnerabilities.
Asked how consumers should protect themselves against the highlighted vulnerability, Mr Yang said: “The main issue is that too many default services are exposed over the wide area network (WAN) interface. Users should change the default passwords on the routers and disable WAN access.”
He added the exact details of the vulnerability will not be released unless the issues have been fixed, to prevent possible attacks from hackers.